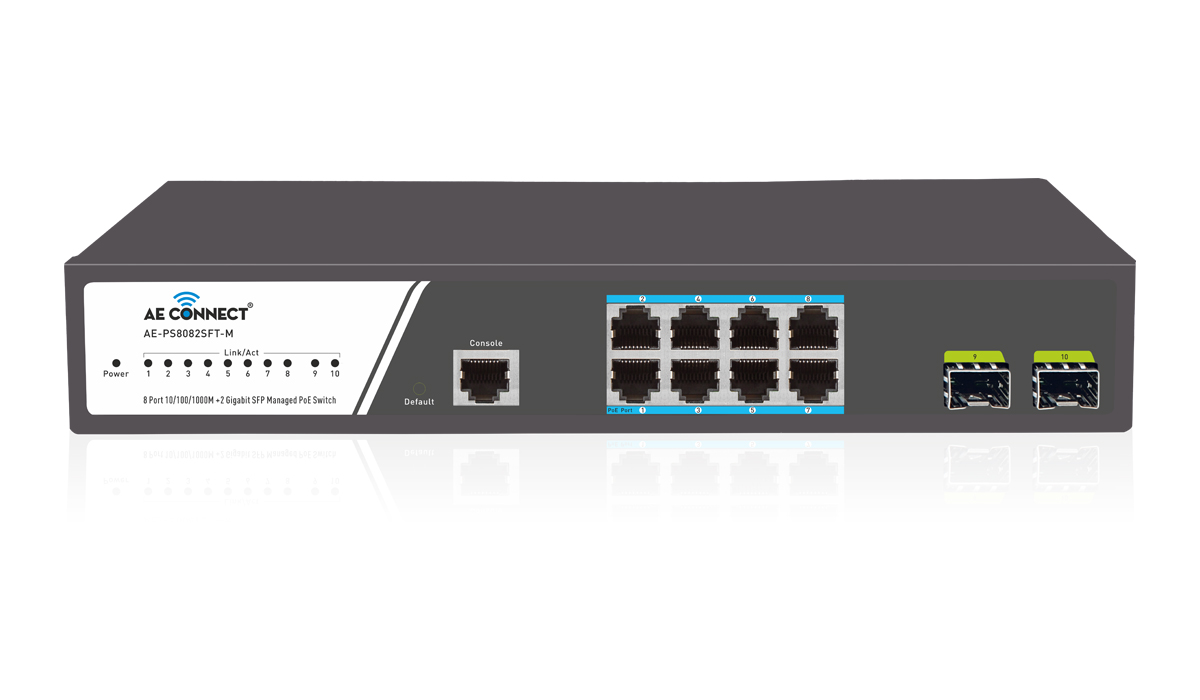
Managed PoE+ Switches
Managed PoE Switch: Nowadays, network efficiency and reliability are more critical than ever. At AE Connect, we understand that when it comes to your network, you deserve more than just the basics. That’s why our managed PoE switches are becoming the top choice among savvy network users.
“Control Your Network, Don’t Let It Control You!”
Unlike unmanaged switches, our smart managed PoE+ switches offer all the features you need and more. They are versatile, reliable, and packed with advantages like administrative controls, real-time network monitoring, and enhanced security.
The AE Connect Advantage: Why Our Managed PoE+ Switches Stand Out
1. Minimizing Network Downtime
Downtime is the enemy of productivity. Our managed gigabit PoE+ switches are designed to keep your network running smoothly, even in the face of challenges. With features like Link Aggregation Control Protocol (LACP), you can boost your bandwidth for high-demand applications without needing to swap out cables. This means a low-downtime, low-latency network that keeps your operations humming.
“Less downtime means more uptime for your business – let’s make every second count.”
2. Lowering Operational Expenses
Cutting costs without compromising quality? That’s the AE Connect way. Our managed PoE+ switches allow you to remotely monitor and manage your network, eliminating the need for round-the-clock onsite staffing at remote locations. This not only streamlines your operations but also significantly reduces your IT overhead.
“Smart management means smarter spending – optimize your resources with AE Connect.”
3. Boosting Security
As security is paramount, our managed PoE+ switches provide the peace of mind you need. With features like MAC address table visibility, you can easily monitor and control who accesses your network, ensuring that unauthorized devices stay out.
“Security isn’t just a feature – it’s a necessity. Protect your network!”
At AE Connect, we’re not just offering a product – we’re offering a solution. Our managed PoE+ switches are here to elevate your network performance, reduce your costs, and keep your data secure.